20 Best Tips For Deciding On Shielded Websites
Wiki Article
The Zk Shield That Powers It: How Zk-Snarks Hide Your Ip And Identity From The World
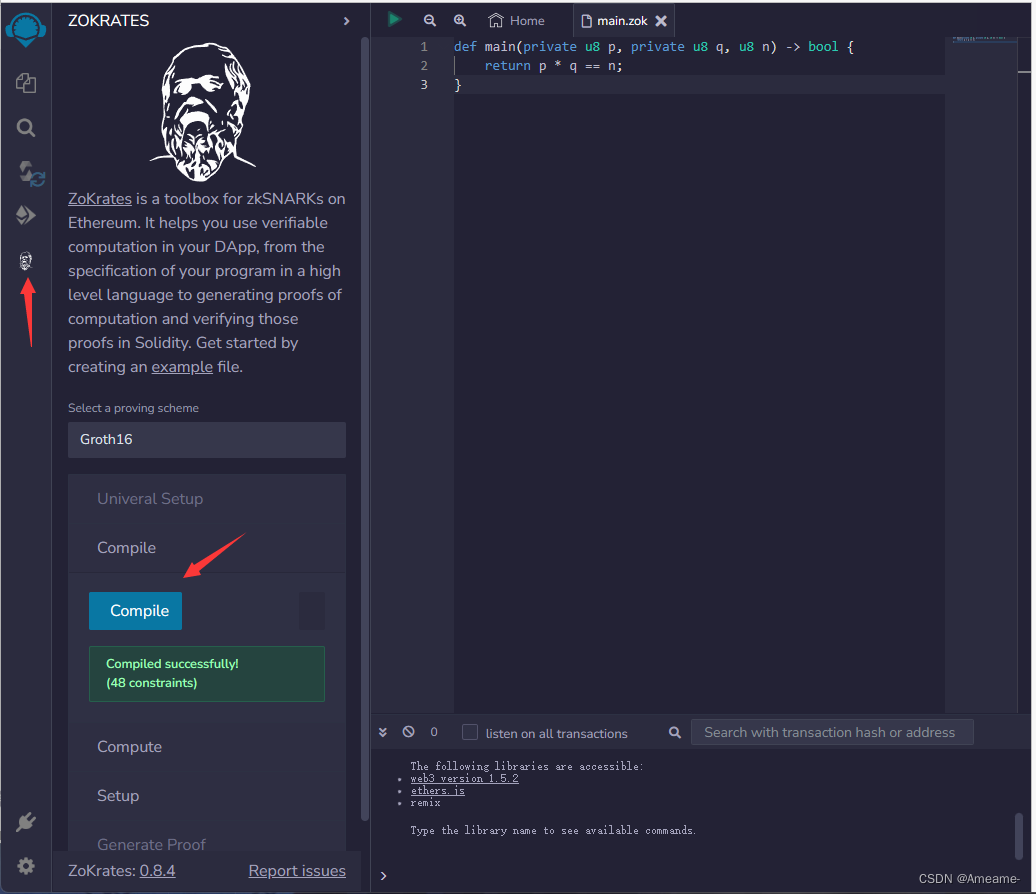
For years, privacy tools employ a strategy of "hiding from the eyes of others." VPNs direct users to another server, and Tor can bounce you between various nodes. They are efficient, however the main purpose is to conceal from the original source by transferring it rather than proving that it does not require disclosure. zk-SNARKs (Zero-Knowledge Succinct, Non-Interactive Arguments of Knowledge) introduce a entirely different approach: you can show that you're authorised to perform an action and not reveal the authority the person you're. For Z-Texts, that you are able broadcast a message for the BitcoinZ blockchain. This network will verify that you're legitimate as a person with a valid shielded address, but it's unable to tell which address you used to send it. Your IP address, the identity of you or your place in the exchange becomes unknowable mathematically by the observing party, and confirmed to the protocol.
1. Dissolution of Sender-Recipient Link
It is true that traditional communication, even with encryption, makes it clear that there is a connection. A observer sees "Alice is speaking to Bob." zk-SNARKs break this link entirely. If Z-Text transmits an encrypted transaction ZK-proofs confirm that it is valid and that the sender's balance is adequate and is using the correct keys. However, it does not disclose the sender's address or the recipient's address. An outside observer will notice that the transaction will appear as a noisy cryptographic signal emanating at the level of the network as a whole, however, it's not coming from any particular person. The connection between two particular individuals is computationally impossible to confirm.
2. IP Address Protection is only at the Protocol Level, not at the App Level
VPNs and Tor protect your IP via routing the traffic through intermediaries. However, the intermediaries then become points of trust. Z-Text's use zk SNARKs guarantees your personal information is not crucial to the process of verification. In broadcasting your signal protected to the BitcoinZ peer-topeer network you are one of thousands of nodes. This zk-proof guarantee that observers are watching stream of traffic on the network they won't be able to relate the text message that is received with the specific wallet that originated it, because the confirmation doesn't include the information. In other words, the IP will be ignored.
3. The Abolition of the "Viewing Key" The Dilemma
In most blockchain privacy applications it is possible to have"viewing key "viewing key" which can be used to decrypt transaction details. Zk-SNARKs that are incorporated into Zcash's Sapling protocol employed by Ztext, allow for selective disclosure. One can show it was you who sent the message but without sharing your IP, any other transactions or any of the contents of the message. The evidence is the only item which can be divulged. The granularity of control is not possible in IP-based systems as revealing that message automatically exposes destination address.
4. Mathematical Anonymity Sets That Scale Globally
With a mix service or a VPN where your privacy is only available to other participants in that specific pool at that exact time. By using zk-SNARKs your privacy is determined is the entire shielded number of addresses within the BitcoinZ blockchain. Because the confirmation proves you are a shielded address in the millions of other addresses, but offers no hint which one, your privacy is as broad as the network. This means that you are not only in an isolated group of people, but in a global gathering of cryptographic IDs.
5. Resistance in the face of Traffic Analysis and Timing attacks
Ingenious adversaries don't read IP addresses; they study the patterns of data traffic. They examine who has sent data, when and how they correlate events. Z-Text's use zk-SNARKs along with the blockchain mempool allows you to separate operations from broadcast. You are able to make a verification offline and publish it afterward for a node to transmit it. When you broadcast a proof, the time it was made for its inclusion in a block is not reliably correlated with the moment you constructed it, leading to a break in timing analysis that usually beats more basic anonymity tools.
6. Quantum Resistance By Hidden Keys
IP addresses are not quantum-resistant. However, should an adversary record your data now, but later crack the encryption that they have, they are able to link the data to you. Zk-SNARKs, as used in Z-Text, protect your keys. The key that you share with the world is never visible on blockchains since the proof proves that you're using the correct key and does not show the key. The quantum computer, in the near future, will view only the proof not the actual key. Past communications remain secret as the password used to sign them was never exposed as a hacker.
7. The unlinkable identity of multiple conversations
With one seed in your wallet that you have, you are able to create multiple protected addresses. Zk-SNARKs can prove that you own one of those addresses without revealing which. That means that you could have ten different conversations with ten different people. And no individual, or even the blockchain itself can connect those conversations with the specific wallet seed. The social graph of your network is mathematically fragmented by design.
8. The elimination of Metadata as a target surface
Regulators and spies often say "we don't even need the contents and metadata." The IP address is metadata. The people you speak to are metadata. Zk's SARKs stand apart from privacy methods because they obscure all metadata that is encrypted. There are no "from" or "to" fields in plaintext. There's also no metadata included in the request. The only evidence is of the evidence. The proof is only what proves that an decision was made, and not who.
9. Trustless Broadcasting Through the P2P Network
When you utilize an VPN for your connection, you're relying on the VPN provider not to track. While using Tor you can trust that your exit node to never be able to spy. By using Z-Text, you transmit your transaction zk-proof to the BitcoinZ peer-to-peer system. A few random nodes. You then transmit the information, then disengage. Those nodes learn nothing because this proof doesn't show anything. They can't even know if you are the originator, as you might be providing information to someone else. The internet becomes a trustworthy source of information that is private.
10. The Philosophical Leap: Privacy Without Obfuscation
Furthermore, zk's SARKs provide the philosophical shift from "hiding" towards "proving the truth without divulging." Obfuscation systems recognize that the truth (your account number, and your identity) is dangerous and must be kept hidden. Zk-SNARKs recognize that the truth doesn't matter. All the protocol has to do is confirm that you have been legitimately authorized. This shift from reactive hiding to proactive insignificance is what powers the ZK security shield. Your personal information and identity aren't hidden. They are essential to the functioning of your network so they're not requested to be transmitted or disclosed. View the most popular blockchain for website advice including encrypted text message, encrypted text message, messenger text message, messages in messenger, messenger to download, private message app, encrypted text message, encrypted text message, messages in messenger, private message app and more.
The Mutual Handshake: Rebuilding Digital Trust in an Zero-Trust World
The internet is built on an implicit network. Anyone is able to email anyone. Anyone is able to follow anybody on social media. This openness, while valuable yet, caused a crisis in confidence. In the case of surveillance, phishing and spam, and harassment are all indicators of a system that connections are not subject to any approval. Z-Text transforms this idea through its mutual handshake. Prior to the first byte data exchanges between two individuals they must both agree on the basis of a connection. this agreement is encapsulated by an encrypted blockchain. Once it's confirmed, the transaction is validated with Zk-SNARKs. A simple step--requiring consent for the protocols level -- re-establishes faith from the ground up. It is like the real world and says that you will not be able to speak with me until you acknowledge me or I'm not able to speak to you until I acknowledge me. In a world of no faith, the handshake has become the basis for all communicating.
1. The Handshake as the Cryptographic Ritual
In ZText, the handshake isn't just a standard "add contact" button. It's a cryptographic event. The Party A submits a connecting request with their private signature and a temporary non-permanent address. Partie B is notified of this request (likely out-of-band or via a public post) and generates an acceptance, which includes their public key. They then both independently obtain a secret shared between them that defines the communications channel. This is a way to ensure that both parties have actively participated in the process and that there is no way for a man-in-the-mi be detected.
2. "The Death of the Public Directory
Spam takes place because email addresses along with phone numbers are all public directories. Z-Text has no directory public. Your address will not be listed on the blockchain; it is hidden inside shielded transactions. Anyone who wants to contact you should have information on you--your public identification, your QR code, a shared secrets to establish the handshake. There's no search feature. This eliminates the major source for unsolicited contact. The person you want to reach cannot be contacted by an contact information is not found.
3. Consent may be considered Protocol It is not Policy
When using centralized apps, the consent is a policy. The user can be blocked after the person contacts you, but you already have their email address. In Z-Text consent is built into the protocol. It is impossible to send a message without the handshake prior to it. The handshake itself is a negligible proof that both individuals have agreed on the connection. This is why the protocol requires consent, rather than just allowing the user to respond to a violators. It is a respectful architecture.
4. The Handshake as a Shielded The Handshake as a Shielded
Since Z-Text employs zk SNARKs, it is a private handshake. If you are able to accept a connection demand, that connection will be shielded. One cannot observe that you and another party have formed a bond. Your social network grows unnoticed. The handshake occurs in digital darkness, visible only to both parties. This is the opposite of LinkedIn or Facebook in which each connection will be broadcast to the world.
5. Reputation Absent Identity
How can you determine who is who to meet? Z-Text's method allows for rise of reputation-based systems that depend on no-disclosure of identity. Since connections remain private, one could get a handshake request from a person with some common contacts. A common contact might be able to verify for them using a cryptographic attestation, with no disclosure of who any of you. A trusting relationship is now merely a matter of time and has no value It is possible to trust someone due to the fact that someone you trust has faith in them, without ever learning their identity.
6. The Handshake is a Spam Pre-Filter
With the requirement for handshakes A determined spammer may theoretically request thousands of handshakes. But each handshake request, like each message, requires at least a micro-fee. Now the spammer has to face the exact same cost at time of connection. Handshakes for a million hands cost the equivalent of $30,000. Even if they do pay an amount, they'll still want you to take them up on. A handshake and a micro-fee are an additional economic obstacle that creates a financial nightmare for anyone who does mass outreach.
7. The Recovery and Portability of Relationships
If you restore your ZText name from the seed phrase all your contacts recover also. But how does the app be aware of who your contacts are absent a central server? Handshake protocols create a minimal, encrypted record in the blockchain. It is a proof that an association exists between two address shields. When you restore, your wallet scans for these handshake notes and rebuilds your contact list. Your social graph will be stored on the blockchain but readable only by you. Your relationships are as portable in the same way as your financial records.
8. The Handshake as Quantum-Safe Engagement
The mutual handshake establishes a joint secret that is shared between two people. This secret is used as keys for upcoming communication. Because handshakes are a shielded event that never exposes private keys, it is resistant to quantum decryption. It is impossible for an adversary to later break into the handshake to see the relationship because the handshake didn't reveal any key public. This commitment is enduring, nevertheless, the handshake is invisibly.
9. Revocation and the Handshake Un-handshake
Insecure trust is easily broken. Z-Text allows an "un-handshake"--a encryption that revokes the connection. When you block someone, your wallet broadcasts a revocation statement. This evidence informs your algorithm that any further messages received from the person you block should be discarded. Since it's on chain, the change is permanent that cannot be ignored by the other party's client. A handshake can be changed but it is identical to the original contract.
10. Social Graph as Private Property Social Graph as Private Property
The mutual handshake makes clear who owns your Facebook or WhatsApp graph. For centralized networks, Facebook or WhatsApp hold the information about what people communicate with who. They mine it, analyze it and then sell it. In Z-Text your social graphs are encrypted and stored on the blockchain. It is accessible only by you. The map is not owned by any company. of your relationships. The handshake ensures that the only record of your connection will be held by you as well as your contact. Your information is secured cryptographically from the world. Your network is the property of you which is not the property of any corporation.
